TLDR
Hackers impersonated an eth.limo team member to trick EasyDNS into handing over account access The attacker changed nameservers twice between 2am and 4am on April 18 before access was restored DNSSEC blocked the attack from causing real damage by rejecting the attacker’s unsigned DNS responses EasyDNS CEO publicly apologized, calling it the company’s first successful social engineering breach in 28 years eth.limo will now migrate to Domainsure, a stricter platform with no account recovery optionEthereum Name Service gateway eth.limo was hijacked on Friday night after a hacker tricked its domain registrar, EasyDNS, using a social engineering attack.
 UPDATE: @eth_limo confirms a DNS hijack after attackers compromised its EasyDNS account via social engineering.
UPDATE: @eth_limo confirms a DNS hijack after attackers compromised its EasyDNS account via social engineering.
Malicious nameserver changes briefly redirected traffic before being reversed.
DNSSEC helped contain the attack — no user impact reported. pic.twitter.com/I6ebk0bL5A
— The Crypto Times (@CryptoTimes_io) April 20, 2026
The attacker pretended to be an eth.limo team member and started an account recovery process with EasyDNS at 7:07 p.m. EDT on April 17. By 2:23 a.m. EDT on April 18, the attacker had flipped eth.limo’s nameservers to Cloudflare. They were then switched again to Namecheap at 3:57 a.m. EDT.
EasyDNS restored the legitimate team’s account access at 7:49 a.m. EDT, ending the roughly five-hour window of exposure.
— ETH.LIMO 
 (@eth_limo) April 18, 2026
(@eth_limo) April 18, 2026
Eth.limo acts as a gateway between regular web browsers and Ethereum Name Service domains. It covers around 2 million .eth domains, including Ethereum co-founder Vitalik Buterin’s personal blog at vitalik.eth.limo.
A successful takeover could have let the attacker redirect users of any .eth site to phishing pages. Buterin warned his followers on Friday to avoid all eth.limo URLs and pointed them to IPFS directly.
How DNSSEC Stopped the Attack
The attacker never got hold of eth.limo’s DNSSEC signing keys. Without those keys, the attacker could not produce valid cryptographic signatures.
DNS resolvers checking the new nameserver responses found they didn’t match the legitimate records. Instead of directing users to the attacker’s sites, resolvers returned error messages.
“DNSSEC likely reduced the blast radius of the hijack. We are not aware of any user impact at this time,” the eth.limo team wrote in its post-mortem.
Buterin confirmed on Saturday that the situation was “all resolved now.”
EasyDNS CEO Mark Jeftovic published his own account of the incident, titled “We screwed up and we own it.” He called it the first successful social engineering attack against an EasyDNS client in the company’s 28-year history.
“This would mark the first successful social engineering attack against an easyDNS client in our 28-year history. There have been countless attempts,” Jeftovic said.
He added that no other EasyDNS customers were affected by the breach.
What Happens Next
Eth.limo will be moved to Domainsure, a service affiliated with EasyDNS that is built for enterprise and high-value clients. Domainsure has no account recovery mechanism, which closes the door that attackers used in this case.
Jeftovic said EasyDNS is still conducting an internal investigation into exactly how the attack was carried out.
This incident is part of a growing pattern. In November 2025, DNS hijacks of decentralized exchanges Aerodrome and Velodrome drained more than $700,000 from users after attackers hit registrar NameSilo and removed DNSSEC from those domains.
Stablecoin protocol Steakhouse Financial disclosed a similar breach on March 30, after OVH support staff were tricked into removing two-factor authentication from its account.
Eth.limo’s service is back online and under the original team’s control.
The post The Attack on eth.limo Shows Why Crypto Websites Are Still Vulnerable to Old-School Hacking appeared first on CoinCentral.


 2 hours ago
6
2 hours ago
6 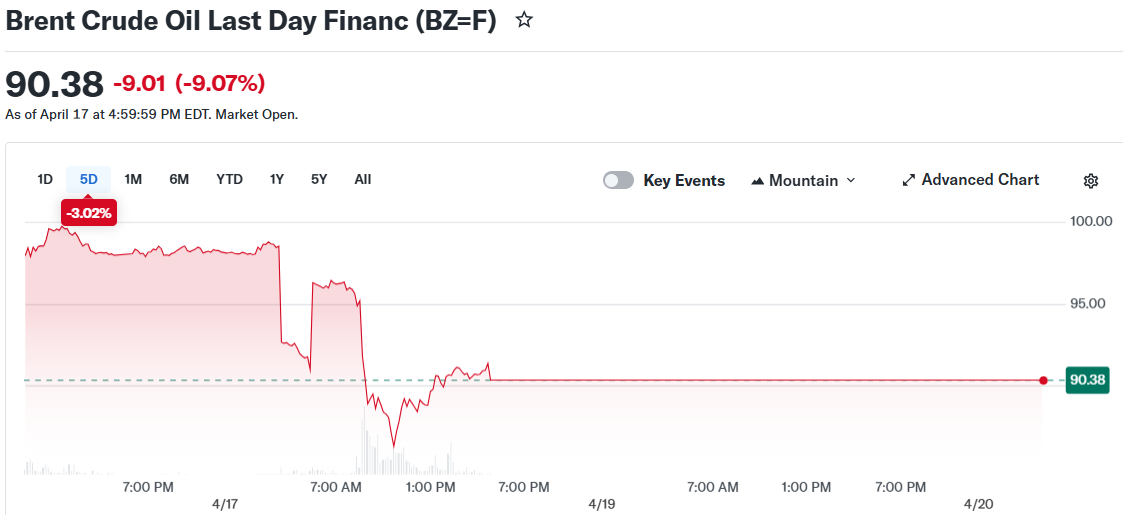




 Bengali (Bangladesh) ·
Bengali (Bangladesh) ·  English (United States) ·
English (United States) ·